unc0ver
The most advanced jailbreak tool.iOS 11.0 - 14.8
View Previous Versions
- Bumped version to 4.3.1 due to a github bug causing an older file to be temporarily available
- Add support for rebooting the userspace for the first time in a jailbreak
- Add support for injecting to the entire userspace
- Add support for looking up or registering services from the sandbox with the cy: prefix for developers
- Reboot the userspace after jailbreaking
- Make major design changes to preserve stock system performance
- Fix random reboots, freezes, memory issues and any known problem that affected system services or apps
- Fix persistent software update blocker on iOS 13 (Works in the jailed state too)
- Fix a design problem that affected the Succession restore tool
- Automatically re-enable software updates when restoring RootFS
- Fix a bug that caused unreliability in starting up substitute
- Fix an issue that broke battery settings and caused extra battery drain
-
Fix issues with system services on A12-A13 (i.e. iMessage notifications)
-
Add iOS 13.0-13.3 support for A8-A11 devices
-
Fix temporary freeze after the jailbreak completed alert
-
You must reboot in order to install this update if you are already jailbroken
-
@Pwn20wnd's substitute bootstrap tooling is used on A8-A11 devices running iOS 13.0-13.3 for battery saving features, improved performance and compatibility reasons
-
There is no particular reason to switch to the unc0ver jailbreak if you are already running the checkra1n jailbreak (Other than the convenience of being able to re-jailbreak your device without a computer)
-
Your jailbreak apps and tweaks will be preserved when switching from the checkra1n jailbreak for A8-A11
-
You can switch back to the checkra1n jailbreak while preserving your jailbreak apps and tweaks but you will need to manually install Cydia Substrate from Cydia after switching back
-
All devices running iOS 13.0-13.3 are now supported
-
The connected Apple Watch may re-sync after jailbreak. It will take around a minute or two and it won't touch your data
- Replace the oobtimestamp exploit by @bazad with the timewaste exploit by @jakeashacks for 99% stage 1 (exploit) reliability on iOS 13.0-13.3
- Fix compatibility issues with iOS 11.0-12.4 and 13.0-13.2.3
- Fully fix App Store on A12-A13
- Fix a bug that affected system services on A12-A13
- Improve the exploit reliability by guiding the user on proper use
- Fix App Store for A12-A13
- Fix push notifications for A12-A13
- Improve reliability for A12-A13 devices on iOS 13.0-13.3
- Full-fledged support for A12-A13 devices on iOS 13.0-13.3 with Cydia and system-wide tweak injection
- Add iOS 12.4.1 support for A12 iPhones (iPads not supported at this time)
-
Full-fledged A12-A12X support with Cydia and system-wide tweak injection
-
Fix Camera on A12-A12X devices
-
Fix GPS on A12-A12X devices
-
Fix App Store purchases on A12-A12X devices
-
Fix Face ID on A12-A12X devices
-
Fix performance issues on A12-A12X devices
-
Fix stability issues on A12-A12X devices
-
Fix reload system daemons issues on A12-A12X devices
-
Fix general stability issues with system services on A12-A12X devices
-
Fix system shutdown on A12-A12X devices
-
Fix system restart on A12-A12X devices
-
Fix USB on A12-A12X devices
-
Fix Xcode debugging on A12-A12X devices
-
Fix a bug in libsubstitute that broke the TetherMe tweak A12-A12X devices
-
Enable full-fledged AMFI/CoreTrust bypass on A12-A12X devices
-
Fix memory management issues on A12-A12X devices
-
Fix tweak injection to MobileSafari on A12-A12X devices
-
Make reload system daemons reload services with launchctl instead of ldrestart
-
Reload system daemons before restarting SpringBoard
-
Correct a problem with reload system daemons when using Substrate (non-A12 devices)
-
Update bundled Cydia to prompt for network access on China devices
-
Rename the bundled mobilesubstrate to match other jailbreaks
-
Update the bundled substitute to 0.1.0
- Fix an issue with the kernel virtual memory access APIs on A7-A8 devices that rendered the jailbreak useless by causing it to fail to copy big kernel data (Error known as: "Unable to copy container profile in kernel memory.")
- Completely redesign and rewrite all jailbreak patches from scratch
- Make the jailbreak patches static and not dynamic--Meaning that the system stability will be completely stock after the jailbreak
- Fix the app crashing on launch when signed with provisioning profiles with non-ASCII characters
- Internally prepare jailbreak patches for full-fledged A12-A12X support
- Make the jailbreak significantly and noticeably more reliable and faster to run
- Add the SockPort 3.0 exploit for improved reliability on iOS 12.4 and devices with low RAM
- Fix SSH support for arm64e devices running iOS12.0-12.1.2
- Make it possible to jailbreak with corrupted SystemVersion.plist on iOS 12.4
- Make the jailbreak perform proper clean up to preserve system stability in case of a failure
- Fix the jbctl command-line utility
- Switch to a new technique for setting the system boot nonce generator that works on all arm64e devices running iOS12.0-12.4 (Thanks to @0x7ff for the idea)
- Fix a bug with the initial Cydia installation getting stuck sometimes
- Significantly speed up the initial Cydia installation process
- Internally prepare upcoming stable substitute support
- Internally prepare Cydia and its resources for full-fledged arm64e support
- Add support for remounting the RootFS as read-write on A12-A12X devices running iOS 12.1.3-12.4
- Adds support for restoring the RootFS on A12-A12X devices running iOS 12.1.3-12.4
- Fixes issues with the jailbreak introduced with the last update
- Fixes iOS 11 support
- Add full-fledged SSH support with root-shell for A12-A12X devices on iOS 12.1.3-12.4
- Add support for arbitrary unsigned code execution on A12-A12 devices on iOS 12.1.3-12.4 (Note: Object files will have to be signed with a CMS blob using the codesign utility)
- Add support for running expired or revoked apps on A12-A12X devices on iOS 12.1.3-12.4
- Fix instant or random reboots after jailbreaking with the SockPuppet3.0 exploit on A7-A12X devices on iOS 11.0-12.4
- Add the updated SockPuppet 3.0 exploit by @umanghere
- Remove the SockPort and SockPort2 exploits
- Update system-memory-reset fix to fix random reboots
- Add Apple to the credits section for development
- Fix error at stage 2 when jailbreaking after updating from a lower firmware while preserving the app data
- Fix the app crashing up on stared up on iOS 11
- Add iOS 12.4 support to the Sock Puppet (A8-A11) and Sock Port (A7-A7X) exploits
- Fix the sandbox swap error when using the exploits that are not SockPuppet
- Add the SockPort 1.5 exploit by @jakeajames for A7-A9X devices (Reliability: ~95% from extensive testing)
- Disable the SockPuppet exploit on A7-A7X due to reliability issues
- Add iOS 12.3~b1 support to the jailbreak (Verified working on iPhone 5s)
- Fix a theoretical reliability bug with SockPuppet
- Replace the SockPort 2.0 exploit with the SockPuppet 2.0 exploit with better reliability and stability on older devices
What's New:
Extensively Tested
Unc0ver has been extensively tested to ensure it's a seamless experience on all devices. Unc0ver works on all devices on iOS versions between 11.0 and 14.3. Below you can find a list of all devices that have been specifically tested.
View Tested Devices
| iPhone 12 Pro Max | 14.3 |
|---|---|
| iPhone 12 Pro Max | 14.2 |
| iPhone 12 Pro Max | 14.1 |
| iPhone 12 Pro | 14.2 |
| iPhone 12 Pro | 14.1 |
| iPhone 11 Pro Max | 13.5.5 Beta 1 |
| iPhone 11 Pro Max | 13.5.1 |
| iPhone 11 Pro Max | 13.5 |
| iPhone 11 Pro Max | 13.3 |
| iPhone 11 Pro | 13.5.5 Beta 1 |
| iPhone 11 Pro | 13.5 |
| iPhone 11 | 14.2 |
| iPhone 11 | 13.5 |
| iPhone 11 | 13.3.1 |
| iPhone 11 | 13.3 |
| iPhone 11 | 13.2 Beta 1 |
| iPhone 11 | 13.2.2 |
| iPhone XS Max | 13.5 |
| iPhone XS Max | 13.5 |
| iPhone XS Max | 13.3 |
| iPhone XS Max | 13.1 Beta 2 |
| iPhone XS Max | 12.4 |
| iPhone XS | 14.3 |
| iPhone XS | 13.5 |
| iPhone XS | 12.4 |
| iPhone XR | 13.3 |
| iPhone XR | 12.2 |
| iPhone X | 13.5 |
| iPhone X | 13.4.1 |
| iPhone X | 12.0 |
| iPhone SE (2020) | 13.5.5 Beta 1 |
| iPhone SE (2020) | 13.5 |
| iPhone SE | 12.1.1 |
| iPhone SE | 11.2.1 |
| iPhone 8 Plus | 13.5 |
| iPhone 8 Plus | 13.2.2 |
| iPhone 8 Plus | 12.3.2 |
| iPhone 8 Plus | 13.3.1 |
| iPhone 8 | 13.5 |
| iPhone 7 Plus | 14.2 |
| iPhone 7 | 13.7 |
| iPhone 7 | 13.5 |
| iPhone 7 | 13.1 Beta 1 |
| iPhone 7 | 13.0 Beta 1 |
| iPhone 7 | 12.0 |
| iPhone 7 | 11.4 |
| iPhone 7 | 11.0 |
| iPhone 6S | 14.2 |
| iPhone 6S | 13.5 |
| iPhone 6S | 12.4.1 |
| iPhone 6 | 12.4.3 |
| iPhone 5S | 12.5.1 |
| iPod Touch | 13.0 Beta 1 |
| iPad Pro | 13.5 |
| iPad Pro | 13.3.1 |
| iPad 7th Gen | 13.2 |
| iPad Mini 5 | 13.4 |
Important Information
unc0ver is designed to be stable and enable freedom from the moment you jailbreak your device. Built-in runtime policy softener allows running code without Apple's notarization and pervasive restrictions. Proper runtime modifications to iOS kernel modify security features as necessary and result in:
No Extra Security Vulnerabilities
unc0ver preserves security layers designed to protect your personal information and your iOS device by adjusting them as necessary instead of removing them. With this security adjusted on your iOS device, you can run your favorite jailbreak apps and tweaks while still being protected from attackers.
Stability & Battery Life
unc0ver is tirelessly developed and rigorously tested with software stability and battery life in mind. If you're experiencing issues with stability or battery life, we recommend searching your device for faulty tweaks.
Reconciliation of Services
Services such as iCloud, iMessage, FaceTime, Apple Pay, Visual Voicemail, Weather, and Stocks, have been reconciled and still work on the device.
Future Software Updates
The ability to apply future updates is retained. Modifications to iOS kernel are done in memory. This results in the jailbroken iPhone, iPad, or iPod touch staying operable when a future Apple-supplied iOS update is installed.
iOS Updates
unc0ver Team strongly cautions against installing any iOS software update that breaks unc0ver as you can't re-jailbreak on versions of iOS that are not supported by unc0ver at that time.
Jailbreak Legality
It is also important to note that iOS jailbreaking is exempt and legal under DMCA. Any installed jailbreak software can be uninstalled by re-jailbreaking with the restore rootfs option to take Apple's service for an iPhone, iPad, or iPod touch that was previously jailbroken.
Detect iOS security issues
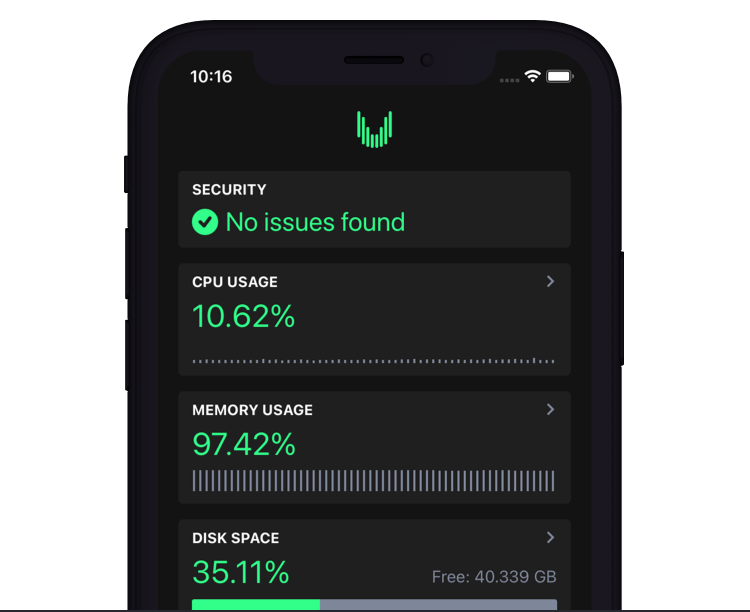
Unveil Security App – Built by the lead developer of unc0ver
The most advanced system and security analysis tool.
Unveil detects real-world iOS security threats with unprecedented methods and provides a customizable dashboard showing 100+ system details including device, system, CPU, memory, disk, network, Wi-Fi, cellular connection, and personal hotspot usage and specifications.
Credits:
 pwn20wnd
Lead Developer
pwn20wnd
Lead Developer
 Sam Bingner
Developer
Sam Bingner
Developer
 Siguza
Developer
Siguza
Developer
 Jake James
Developer
Jake James
Developer
 Ubik
Designer
Ubik
Designer
 Dennis D. Bednarz
Logo Designer
Dennis D. Bednarz
Logo Designer
 exDeveloper
UI Dev
exDeveloper
UI Dev
Thanks to: pattern-f for the CVE-2021-30883 exploit (Used for iOS 14.6-14.8) Brandon Azad for the timestamp bug. Ned Williamson for the socket bug.